Key Takeaway
- Identity verification alone does not stop modern communication-based attacks.
- CLEAR focuses on KYC and one-time proof of identity; Traceless protects ongoing business communication.
- Traceless enforces trust during conversations and workflows—where real damage actually occurs.
Social engineering security failures don’t usually happen at login. They happen mid-conversation in Slack, Teams, tickets, and service desks—when someone convinces a human to take a risky action.
That distinction is at the heart of how modern identity attacks succeed; essential when comparing CLEAR's CLEAR1 and Traceless. When it comes to preventing vishing, account takeovers, secret sprawl, ShinyHunters, and Scatter Spider the solution decision is about where and when identity is enforced.
The Shared Question — Very Different Answers
Both Traceless and CLEAR exist to answer one critical question:
Is the human making this request actually who they claim to be?
CLEAR: Identity Verification (KYC)
CLEAR is built around Know Your Customer (KYC) and high-assurance identity proofing. Its model is familiar:
- Airports and stadiums
- Workforce onboarding
- Healthcare and financial services
- Identity badges and blue-check-style verification
CLEAR establishes identity as a one-time transaction; scan an ID, take a biometric selfie, verify against an authority, and move on. Once trust is granted, CLEAR typically disappears from day-to-day operations.
This makes CLEAR adjacent to banking and compliance-heavy environments, where proof of identity must be durable, auditable, and regulator-friendly.
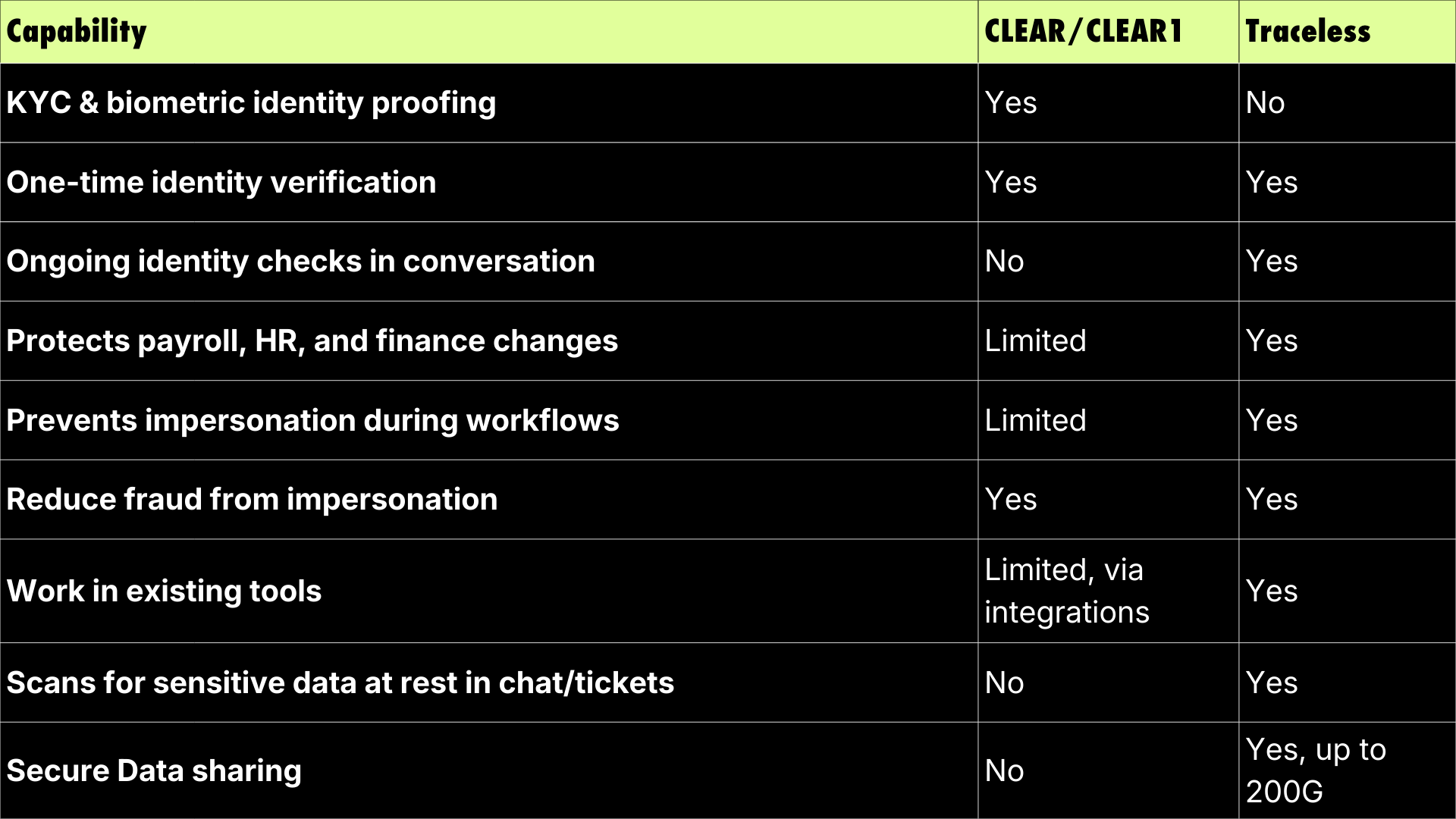
CLEAR1 and Traceless Capability Comparison
Traceless: Identity Verification for Ongoing Communication
Traceless is built for operational support workflows and replaces identity-only security:
- Employees and vendors communicate constantly
- High-risk requests arrive through chat, tickets, and calls
- Voice AI, phishing, and impersonation attacks exploit trust after onboarding
Traceless focuses on regular, contextual identity verification inside business communication, not one-time proofing.
It protects conversations like:
- Payroll or banking changes requested in Slack
- Privilege changes through IT tickets
- Vendor requests inside shared channels
- Sensitive approvals handled informally
Traceless verifies who you’re talking to, in the moment, without forcing users to leave their workflow or scan government IDs.
Traceless protects businesses every time people communicate.
As work becomes more remote and conversational, attackers become more convincing.
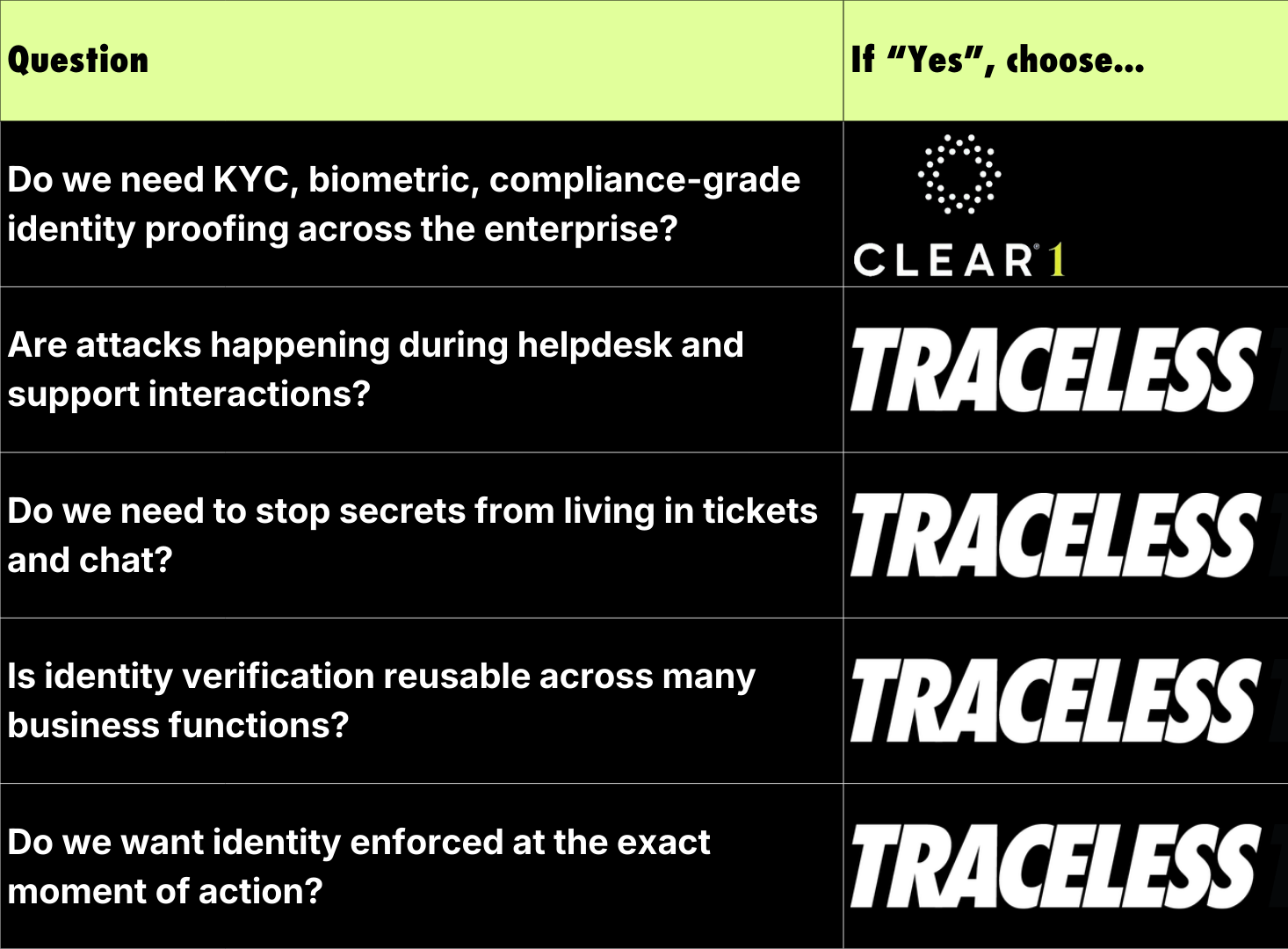
CLEAR1 or Traceless Buyer's Framework
Why is Traceless a true CLEAR1 alternative for security?
If your risk originates in tickets, chat, or service desks → Start with Traceless. Buyers consistently choose Traceless when the real problem is operational.
CLEAR1 verifies identity. Traceless enforces security.
CLEAR is the identity assurance engine, strong proofing and biometric verification across enterprise and regulated environments.
Traceless is the workflow security layer, making verification unavoidable and keeping sensitive data from persisting in tools people already use.
Is Traceless a replacement for CLEAR?
Not always. CLEAR is ideal for KYC and compliance-driven identity proofing. Traceless replaces CLEAR when the primary risk is communication-based attacks.
Does Traceless use biometrics or ID scans?
No. Traceless focuses on low-friction, contextual verification inside conversations.
Which teams benefit most from Traceless?
Finance, HR, IT, MSPs, and security teams managing sensitive requests through chat and tickets.
What problem does Traceless uniquely solve?
Protecting business communication after trust is granted—where modern social engineering attacks actually succeed.