Secure high-risk interactions.
Trigger on-demand identity verification and safely exchange sensitive data across phone, email, chat and ticketing platforms.
Protect against social engineering and AI impersonation. Built for help desks, customer operations and vendor payment teams. Trusted by:





Since 2019
1M+
TRANSACTIONS SECURED TO DATE
$50B+
IN PREVENTED BREACH COSTS
15,000+
ACTIVE USERS
THE PROBLEM
Cybercriminals don't just hack systems. They hack people.
- 74% of breaches involve a human element — social engineering, vishing, credential theft, phishing, and impersonation.
Verizon Data Breach Investigations Report, 2026
- Voice-based impersonation is rapidly scaling — 300–400%+ growth, driven by AI voice cloning.
Pindrop Voice Intelligence & Security Report, 2025
- Average cost of a data breach is $4.45M — driven by compromised credentials and sensitive data exposure.
IBM Cost of a Data Breach Report, 2025
THE GAP
Current tools and practices don’t address your risk
- Access ≠ identity; hackers are bypassing login identity challenges, identity verification is inconsistent and high-friction.
- Sensitive data persists in the wrong places. Common DLP solutions don’t address residual exposure in email, tickets, and chat logs.
- No audit trail — high-risk interactions aren’t well tracked, policies are inadequate at key attack surfaces, secure behavior isn’t incentivized.
THE SOLUTION
Traceless secures every high-risk interaction
Protect sensitive exchanges across messaging, email, and real-time communication — without disrupting how teams work.
Traceless Verify
On-demand, bidirectional, one-touch identity verification, internal and external.

Traceless Data
Encrypted, expiring links to exchange sensitive data without persistent exposure.
Traceless Protect
Automated identity verification and data handling. Agentic policy enforcement.
Escalations, Audit Logs + Reporting
Audit-ready, every interaction logged. Reporting to track failures, near-misses, adoption, compliance, and risk reduction.
Change Management Support
Policy recommendations, education, adoption support, compliance mapping.
HOW IT WORKS
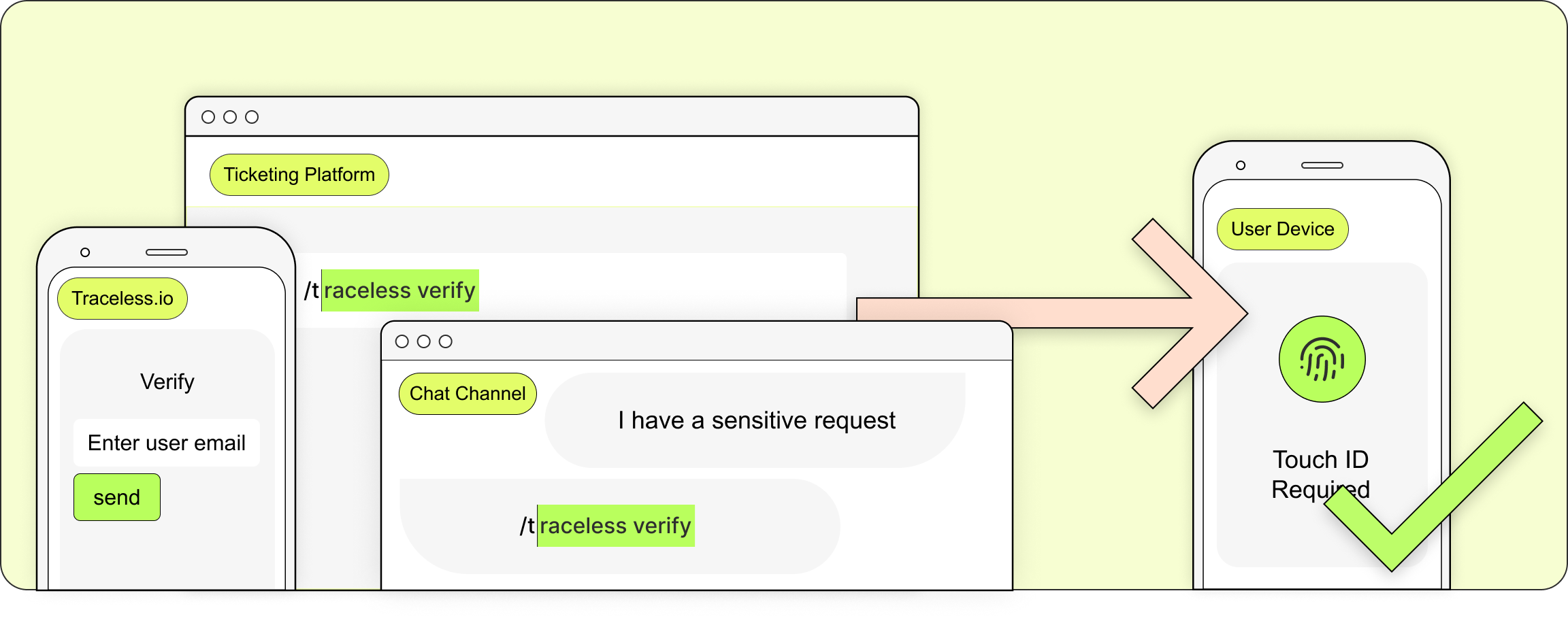
Traceless Verify: On-demand Identity Verification
Verify identity at the moment it matters — preventing account takeover and privilege escalation. Bi-directional across internal and external interactions.
- Easily deployed in the app or by a keystroke in chat or ticket platform.
- Low-friction for all parties, deploy at key moments of high-risk action or exchange.
- Strengthened by leveraging a wide range of verification mechanisms, including biometric passkeys, Verified ID, Okta, Duo, Entra and more.
HOW IT WORKS
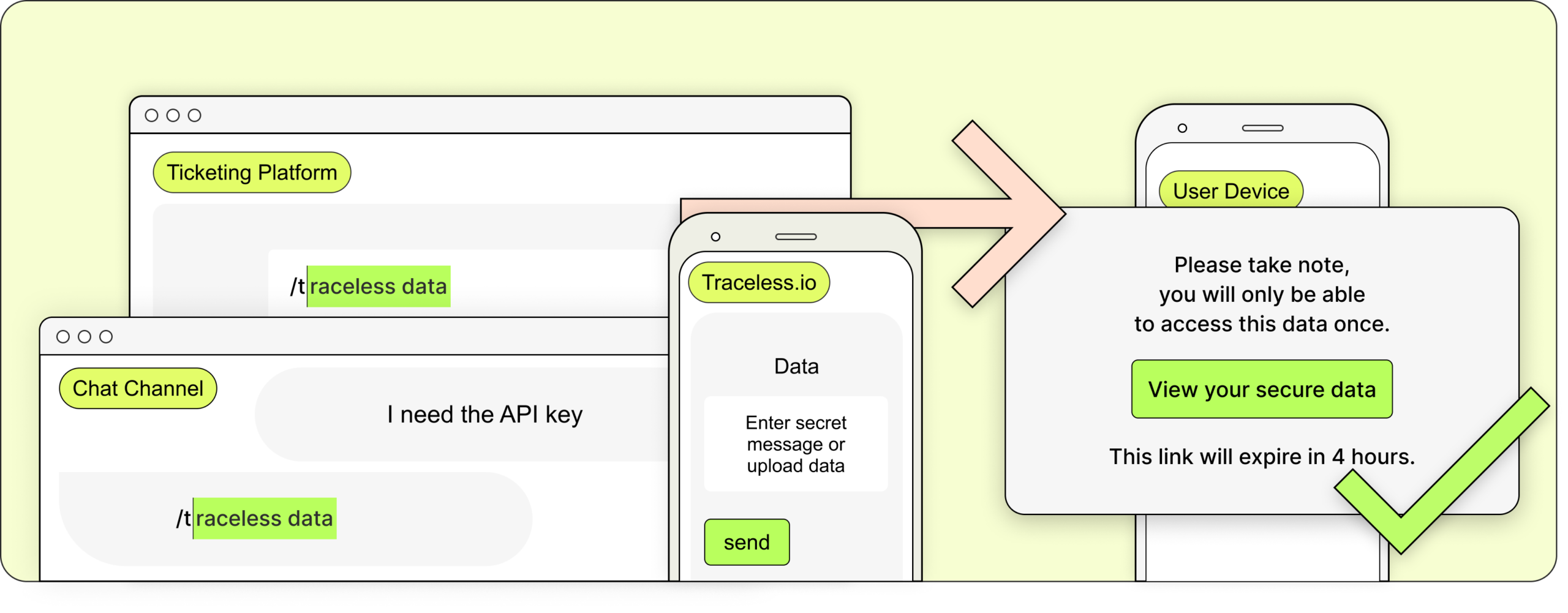
Traceless Data: Secure Sharing
Send and request sensitive messages and data securely with encrypted, expiring links — leaving nothing behind.
- Create a magic link in the app or with a keystroke in your chat or ticket platform. Flexibly configure data security requirements.
- Trace data requests protect customers and partners by facilitating exchange without persisting sensitive data in their channels.
- Strengthened by leveraging a wide range of verification mechanisms, including biometric passkeys, Verified ID, Okta, Duo, Entra and more.
HOW IT WORKS
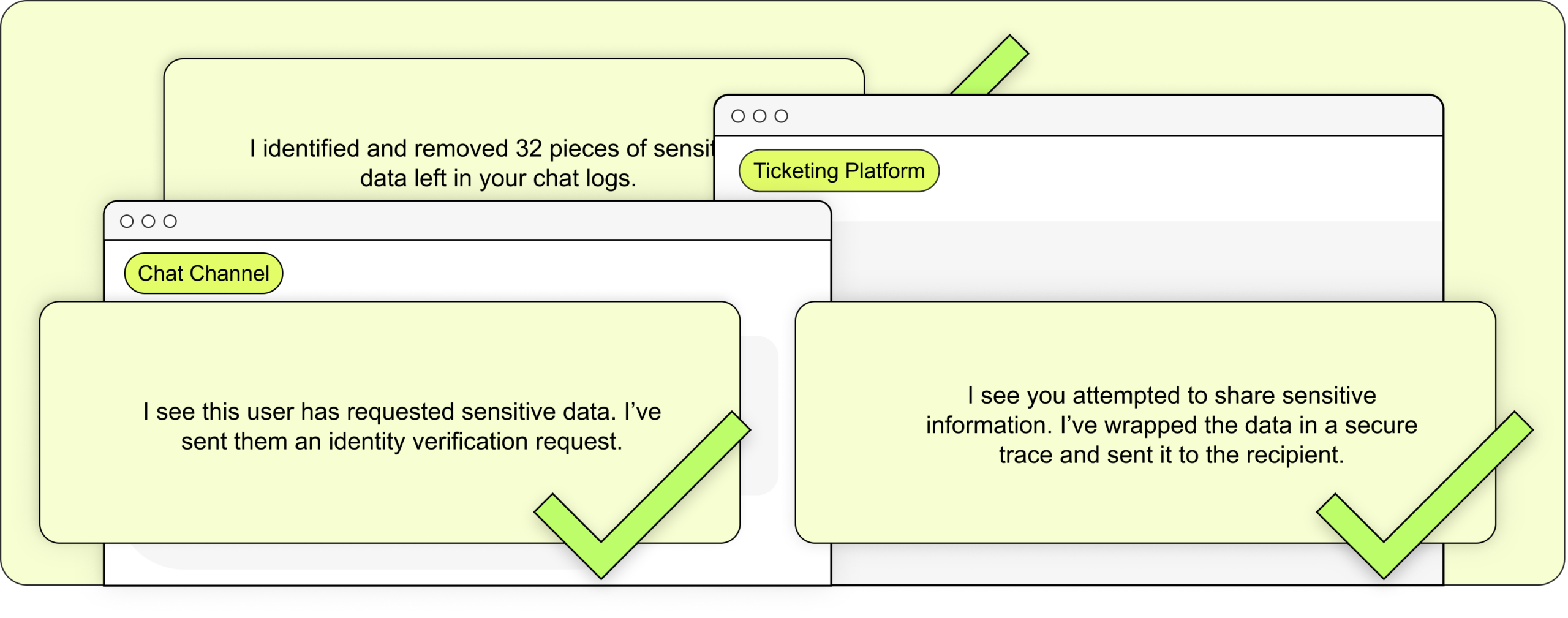
Traceless Protect: Agentic DLP
Real-time detection and enforcement that identifies sensitive requests and secures them automatically across Slack, Teams, and ticketing systems — before they become breaches.
- Driven by a SLM (Small Language Model) unique to, and trained by, your organization.
- Scans for and removes persistent, sensitive records on your communication channels and ticket platforms.
- Agentic AI enforces your security policies in realtime.
Integrations
Works in the systems your team already uses
More than 15 integrations and always building. API-native.



OPERATIONAL IMPACT
Efficiency, consistency, accountability
- Security without friction, no more manual, out-of-band verification loops.
- Flexible tools for managing the unpredictable reality of urhent, ad hoc requests.
- Program visibility without reliance on manual record keeping.
USE CASES
Where to deploy Traceless first
IT Helpdesk
Stop social engineering at the point of request. Verify identity before password resets, access changes, or privilege escalation.
HR support
Protect employee data in motion. Verify identity and secure sensitive exchanges for payroll, benefits, and PII requests.
Customer service
Replace weak authentication with certainty. Verify customers before exposing account data or executing high-risk actions.
Finance + payments
Eliminate payment fraud at the source. Verify identity and instructions before any transfer, change, or approval.
Vendor engagement
Trust, but verify—every time. Authenticate vendors and secure sensitive exchanges across external workflows.
Privileged communication
Secure your highest-risk interactions. Verify participants and protect sensitive data in executive, legal, and IT communications.
INDUSTRY
Built for enterprise and high-risk, regulated environments
Managed IT Services (MSPs)
Your help desk is your biggest risk surface. Verify identity and secure client interactions in real time—supporting SOC 2 and client security requirements.
Financial Services
Stop account takeover and wire fraud at the point of interaction. Enforce identity verification and secure exchange aligned to FFIEC and GLBA.
Healthcare
Protect PHI in motion across support and admin workflows. Verify identity and secure exchanges to support HIPAA compliance.
Legal + Accounting Services
Secure privileged client communications. Verify identity and exchange sensitive data without relying on email—aligned to AICPA and ABA guidance.
Government
Enable trusted, auditable interactions across agencies and constituents. Support NIST and Zero Trust with real-time verification and secure exchange.
Construction + Manufacturing
Prevent vendor and payment fraud across distributed teams. Verify identity and secure sensitive exchanges in operational workflows.
COMPLIANCE AND INSURANCE
Audit readiness
- Aligns to SOC 2, NIST, CIS, ISO, HIPAA, GDPR, CMMC 2.0, Mitre Attack, Mitre Defense. Contact us for detailed compliance mapping support.
- Immutable audit record for identity verification and secure data exchange.
- Scans for and removes persistent, sensitive records on your communication channels and ticket platforms.
GET STARTED
Secure every high-risk interaction
Rapid deployment. Immediate risk reduction.