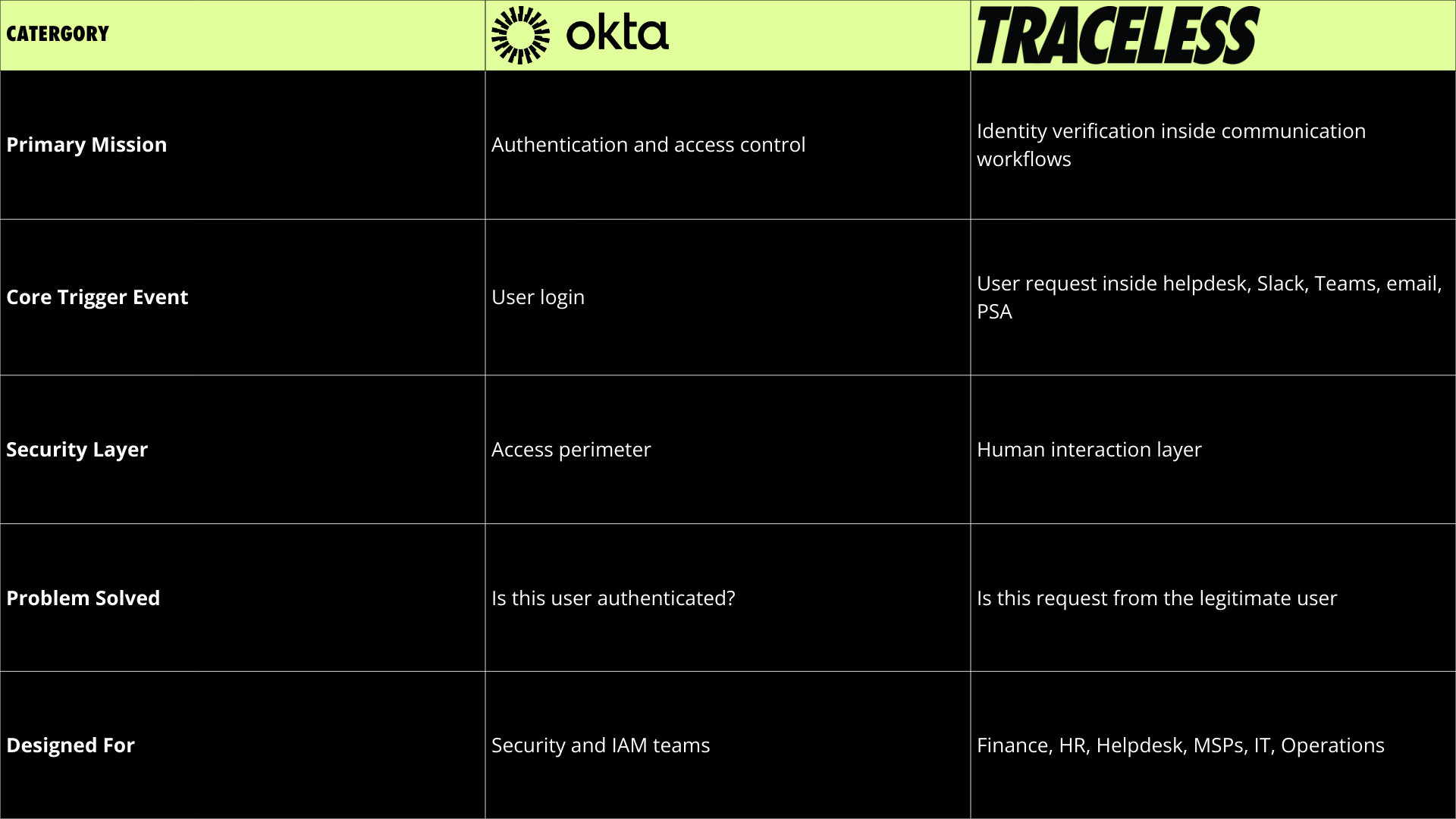
Key Takeaway
- Authentication and verification are different control points in the identity lifecycle
- Okta secures system access. Traceless secures sensitive business communication
- Some overlap exists in adaptive risk and MFA, but workflow context is the dividing line
- The strongest security posture layers authentication and verification, not one or the other
Identity Risk Has Moved Downstream
Over the past decade, identity platforms like Okta have transformed enterprise security with single sign on, multi factor authentication, adaptive policies, and risk based access controls. These capabilities have dramatically reduced credential based attacks.
Today’s breaches increasingly occur after authentication, inside trusted collaboration channels, support workflows, and IT service desks.
Authentication happens once. Support requests happen constantly. How do organizations protect themselves from this shift?
That distinction is where Okta and Traceless converge, diverge, and partner.
Login Security vs Action Security
Okta answers a foundational question:
Is this user authenticated to access this system?
Okta’s Core Strength
Okta is strongest at the perimeter of application access:
- SSO and centralized identity management
- MFA and device trust
- Adaptive access policies
- Governance and lifecycle management
Traceless answers a different question:
Is this request and communication coming from the legitimate user right now, inside this workflow?
Traceless’s Core Strength
Traceless is strongest at the human interface layer, where impersonation risk is highest.
- Enterprise identity verification
- Requesting validation inside collaboration and communication channels
- Behavioral and contextual trust signals
- PSA and ticket level orchestration
- Secure data sharing (up to 200G)
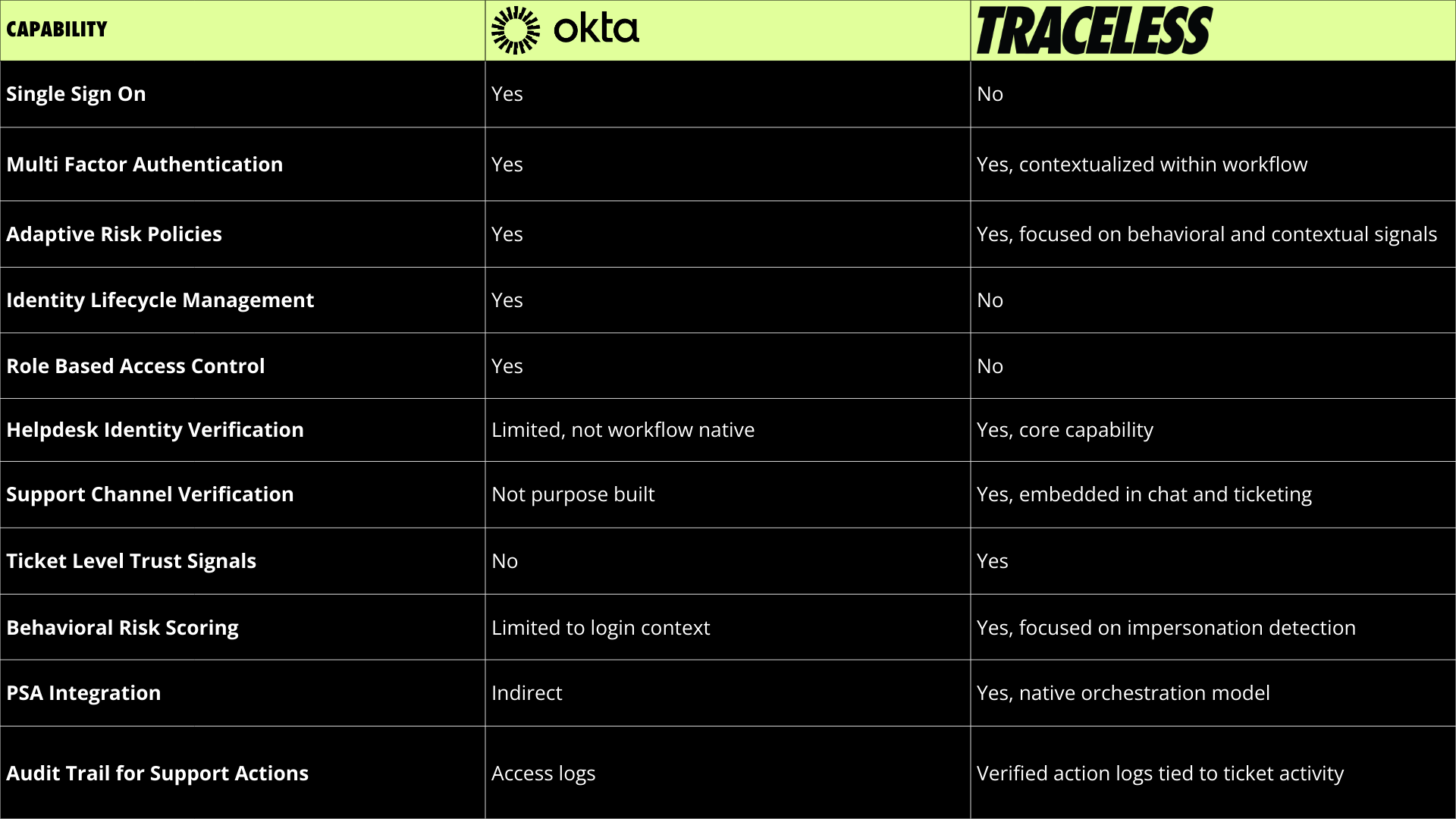
Where Okta and Traceless Converge
Both platforms aim to increase identity confidence and reduce fraud. Both reduce social engineering risk.
There is also tactical convergence in three areas:
- Risk signals
- MFA and second factor validation
- Adaptive policies
Helpful Tip
In some environments, organizations attempt to stretch Okta’s adaptive MFA to handle support verification. In low complexity environments, that may be sufficient. In high volume helpdesk or MSP workflows, the friction and operational overhead quickly become visible.
Where We Partner
The most resilient architecture layers authentication and verification.
A secure pattern looks like:
- Okta establishes secure login and device trust
- Traceless verifies high risk support requests in Slack, Teams, email, or PSA systems
- Verification signals are embedded directly into ticket workflows
- Sensitive actions are approved only when both authentication and verification criteria are met
Okta & Traceless: Integration
This model reduces account takeover via helpdesk, insider impersonation, privileged escalation requests, fraudulent password resets. It also improves operational efficiency because verification becomes workflow native rather than manual.
When to Use Okta or Traceless, or Both
This chart helps security and IT leaders decide based on maturity, risk profile, and workflow complexity.

Traceless protects businesses' Revenue with Verification
As work becomes more remote and conversational, attackers become more convincing.
FAQ: Authentication and Verification Explained
1. What is the difference between authentication and identity verification?
Authentication confirms that a user can access a system, typically using credentials and MFA.
Identity verification confirms that a specific request or action is genuinely initiated by that user at that moment, especially inside support and communications.
2. Can Okta handle help desk identity verification?
Okta provides strong authentication and adaptive access controls at login.
However, help desk impersonation often occurs after login, inside email, Slack, Teams, or ticketing systems. These workflows typically require purpose built verification embedded directly into support processes, i.e. Traceless.
3. Does Traceless replace Okta?
Not always.
Okta establishes secure access to systems.
Traceless extends identity assurance into support workflows and high risk operational requests.
They operate at different layers of the identity lifecycle.
4. When should an organization use both Okta and Traceless?
Organizations should layer both when:
• MFA and SSO are already deployed
• Helpdesk impersonation risk is increasing
• MSP environments manage multiple tenants
• Sensitive actions occur via ticketing systems
• Audit requirements require verified intent logs
5. What types of attacks happen after authentication?
Common post-login attacks include:
• Sensitive data sharing
• Fraudulent password reset requests
• Privileged escalation via support
• Insider social engineering
• Chat based impersonation in Slack or Teams
6. Is MFA enough to prevent help desk fraud?
MFA significantly reduces credential based attacks.
It does not inherently validate that a support request is legitimate when submitted via email, chat, or ticketing platforms.
Verification inside workflow reduces this risk.