Payroll Fraud Starts Before Payday
Payroll fraud starts before payday. It starts in the conversation before the system change, the call before the reset, and the leftover context that makes a fake request feel routine.
A real payroll fraud case
In December 2025, Binary Defense’s threat research group, ARC Labs, investigated an incident that ended with a physician’s paycheck landing in someone else’s account. The final move looked low-tech: a phone call backed by stolen context.
By the time that call happened, the attack was already in motion. The attacker began with compromised credentials for a shared mailbox at a healthcare facility. From there, they read through enough internal messages to learn how the physician spoke, who they reported to, and what kind of access they needed to see patients. That context was the payload. The next step was a call to the help desk, urgent in tone, claiming the physician could not log in and had patients waiting. The name checked out. The access level checked out. The help desk reset the password and MFA token.
After that, the attacker logged in through the organization’s own virtual desktop infrastructure, so the traffic looked like any other internal session. They registered new authentication devices and opened Workday. A few clicks later, the direct deposit details were changed. The fraud was not caught until the physician asked why they had not been paid.
The paycheck was the target. The workflow was the attack path.
Payroll fraud is growing
This case is not a one-off. The FBI’s 2025 Internet Crime Report logged more than one million complaints and nearly $21 billion in reported losses, a 26 percent jump from the year before. Business email compromise alone accounted for more than $3 billion of that total. AI-assisted scams add another layer by making phishing language, voice impersonation, and internal-looking messages easier to produce at scale.
Payroll diversion sits inside that same trend. Microsoft has tracked a cluster of attacks it calls Storm-2657, often referred to as Payroll Pirates, targeting Workday and other HR SaaS platforms. The pattern is consistent. Compromise the email account, take over the HR profile, change the banking details, suppress the warning notifications, and wait for payday. None of it requires a software exploit. It requires a workflow that moves faster than its verification.
Why HR Is exposed
Workflows do not move that fast by accident. The speed comes from pressure that shows up in normal HR work every day. A message comes in near the end of a busy workday: "Hey, can you update my direct deposit before the next run?" It sounds routine. It also sounds urgent enough to push someone into acting quickly, because a missed deadline can mean a missed paycheck.
HR and payroll workflows are built to be fast, familiar, and responsive. Employees cannot wait through a full investigation every time they need help with pay, so teams rely on workflow signals to decide whether a request is real. Where did it come from? Does the timing make sense? Does it fit a real employee need? Attackers know those signals exist and shape their requests to match them. The trust side is impersonation: looking like the right person. The context side is what makes the lie feel believable: knowing when to ask, what to ask for, and how to make the request fit the normal rhythm of the work.
AI lowers the skill bar for that kind of impersonation, so attackers no longer need deep technical skill to sound convincing. But the disguise is only the surface. The structural gap underneath is what the attacker actually exploits. Attackers do not need much context at once. They piece together believable stories from a past onboarding form, an old benefits question, or a chat with a manager about an issue that was resolved months ago. None of those feel sensitive once the task is done, which is exactly why they stay accessible.
That is residual data risk: old details, quietly available in everyday tools. The same email archives, ticket histories, chat logs, and shared drives that run the daily work also hold the small specifics that make a fake message feel real. The junk drawer no one wants to clean is also the place attackers come looking for spare keys.
The answer is not to make HR suspicious of every request. It is to reduce the leftover context attackers can reuse, then verify sensitive actions before trust becomes a payroll change.
How Traceless helps that change happen
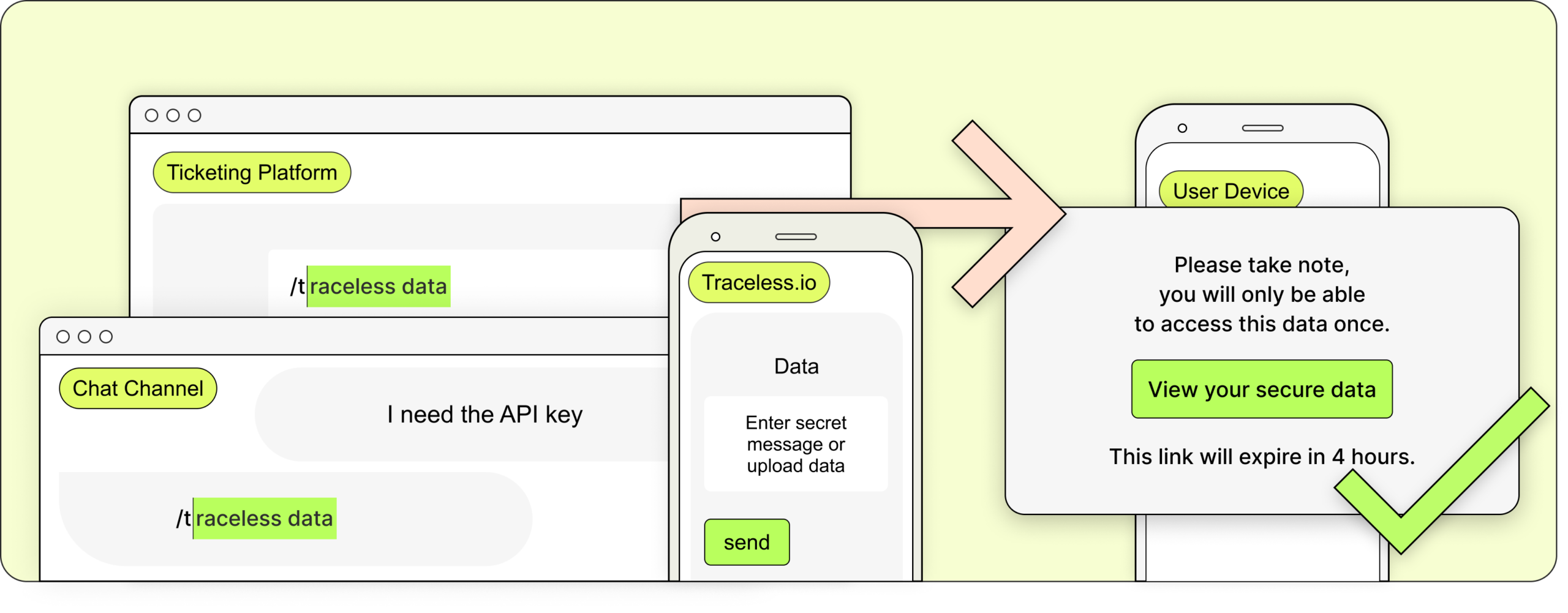
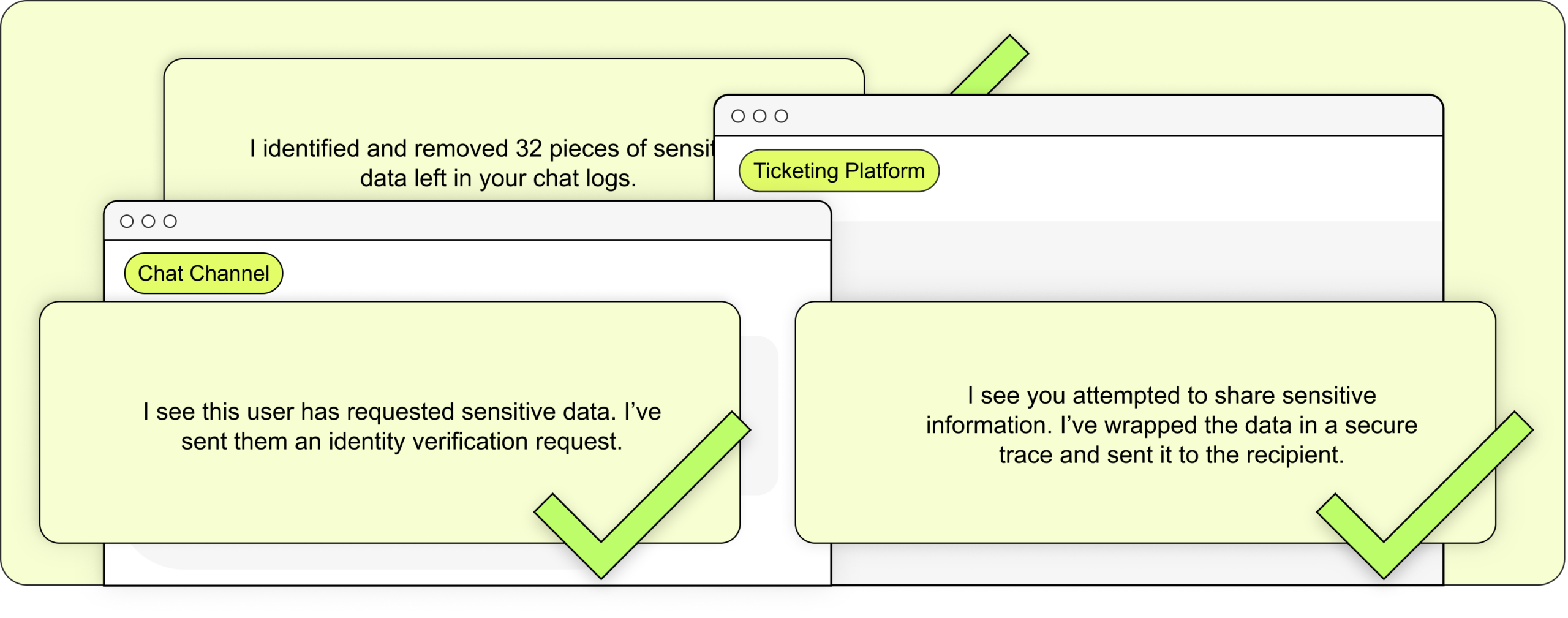
That protection starts by changing what happens to sensitive information after the task is done. In a normal HR workflow, payroll forms, identity details, and employee documents often remain scattered across inboxes, chats, tickets, and shared folders long after anyone needs them. Traceless Data gives that information a shorter life through expiring Traces: available while the work is active, then removed when the work is done. Traceless AI strengthens that same protection while the work is still happening, helping flag sensitive details before they become leftover context an attacker can reuse later.
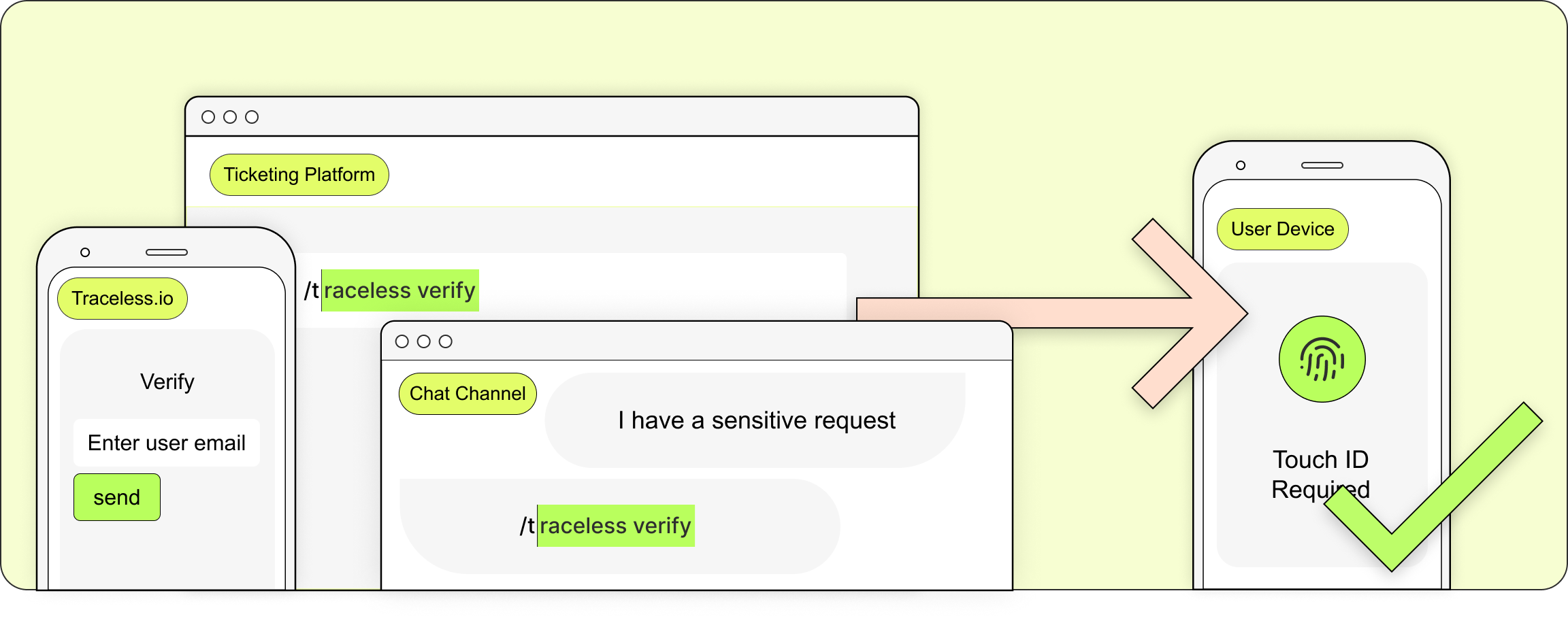
Then, when someone does request a sensitive action, Traceless Verify protects the decision point. A direct deposit change should not move forward just because the message sounds believable or the person is already logged in. Verify can trigger an MFA prompt before the change is approved, so the workflow waits on confirmed identity instead of trust built from stolen context. That is the step the Binary Defense case never had.
Final Takeaway
Payroll fraud starts before payday. It starts in the conversation before the system change, the call before the reset, and the leftover context that makes a fake request feel routine. HR work moves fast across channels by design. That speed is its strength, but it also creates openings when trust moves faster than verification.
Behind all of this is one simple goal: make the safer action the easier action, so speed does not quietly become blind trust.
Prevent impersonation attacks
Start with one integration, validate quickly, and expand across your environment.